Also consider…
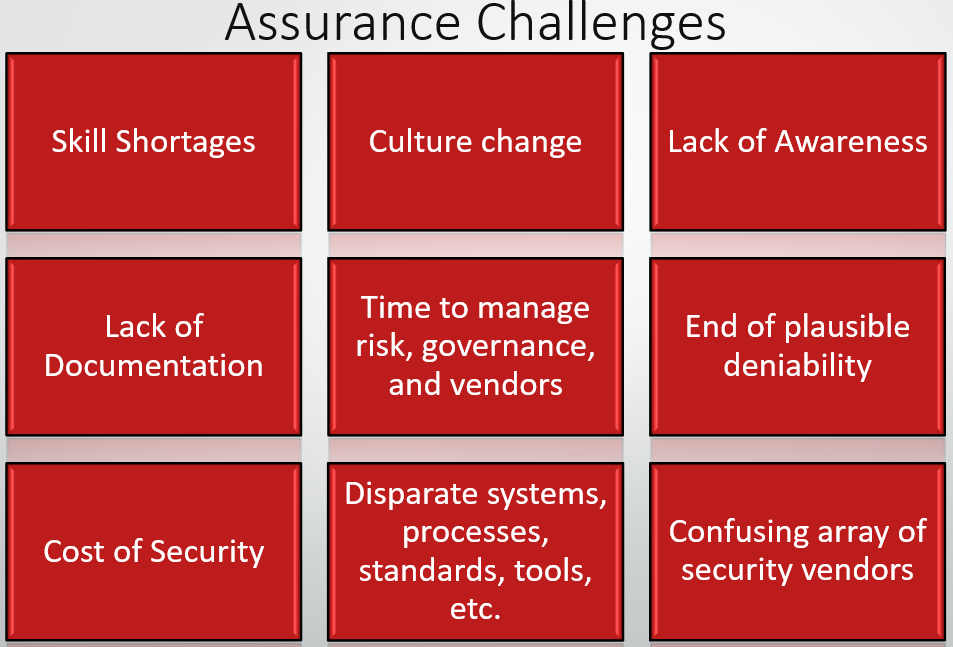
- Customers, insurers, stakeholders are asking about your security status
- Malicious actors can destroy an unprepared business
- Time-consuming compliance oversight including, internal & external audits
- Acquisition, configuration, implementation, and management costs
- Governance, Risk, and Compliance program development time
- Understanding security posture & requirements
- Difficult to compile complete, accurate, and timely evidence